Dive deep into the complex world of module injection, a potent technique with the capacity to alter application behavior. We'll investigate its nuances, uncovering the tactics employed by both security researchers and attackers. From susceptible code analysis to sophisticated mitigation techniques, this deep dive will equip you with the knowledge t
 Tia Carrere Then & Now!
Tia Carrere Then & Now! Christina Ricci Then & Now!
Christina Ricci Then & Now!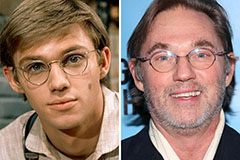 Richard Thomas Then & Now!
Richard Thomas Then & Now! Mary Beth McDonough Then & Now!
Mary Beth McDonough Then & Now! Nadia Bjorlin Then & Now!
Nadia Bjorlin Then & Now!